ConnectWise Automate MySQL 8.4: What MSPs need to know

ConnectWise Automate now supports MySQL 8.4. In this blog, we’ll look at what this means for MSPs and what the upgrade process is like. What’s New in MySQL 8.4? MySQL 8.4 is the latest long-term support (LTS) branch. It’s the successor to MySQL 8.0, which goes end-of-life in April 2026. Being an LTS branch, its […]
ConnectWise Ends MySQL 5.7 Support: What MSPs Need to Know

In January, ConnectWise announced they are ending support for MySQL 5.7 in Automate. In this blog, we’ll explore what that means and what actions MSPs need to take. Already End-of-Life You might be aware that MySQL 5.7 reached end-of-life in October 2023. It stopped receiving security updates, and for security and insurance/compliance reasons, your MySQL […]
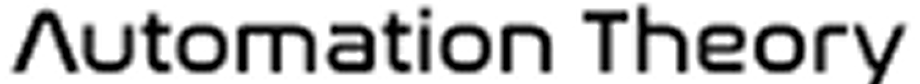
ConnectWise Automate Firewall ports: The complete guide
ConnectWise Automate firewall ports have changed over the years, and many partners still have ports open that aren’t required (or are dangerous to have open). Since the guidance has changed over the years, we wanted to create an updated guide that covers how the protocols work, along with what firewall ports are required (and what […]
Cloud Automate security isn’t necessarily better
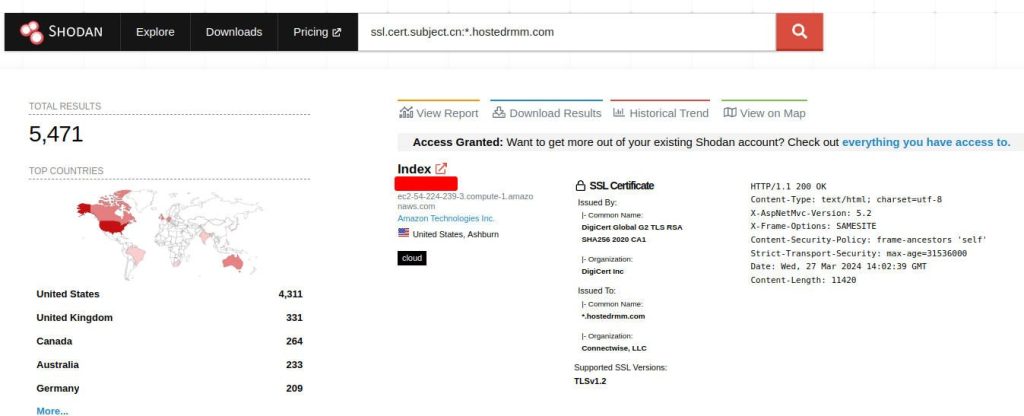
Is Cloud Automate (aka Hosted RMM) more secure? In light of the recent ScreenConnect vulnerability, ConnectWise has touted the security benefits of using their cloud-based products. The software and features are approximately the same no matter the hosting configuration (some space restrictions notwithstanding), so ultimately, the hosting decision is a business decision. However, when it […]
Scaling ConnectWise Automate with a 3-way split

RMM scaling is an increasingly common conversation as M&A transactions abound in the MSP space. As companies merge (or experience rapid organic growth), questions arise regarding how scalable Connectwise Automate is. The initial answers might seem discouraging, but we’d like to set the record straight: it’s possible to scale Automate much larger than you’d initially […]
Connectwise Automate IP Restrictions: The good, bad, and ugly

IP restrictions for Connectwise Automate were released in patch 2022.11. This long-awaited feature has some nuances worth noting in the implementation, which we’ll discuss below. But first, let’s review the good parts of this feature. The good: IP restrictions are possible with Connectwise Automate Right off the bat, it’s worth noting that this much-requested feature […]
State of Connectwise Automate Security 2022

We’re approaching the one-year anniversary of the Kaseya VSA attacks, and here at Automation Theory, we were curious about the state of security for Connectwise Automate. Many MSPs we work with are concerned about similar threats and attacks against the Automate platform. To this end, we wanted to track and provide meaningful reporting about the […]
How to defend ConnectWise Automate in a Cyberwar

Recent world events lead many to conclude that cyber-attacks may be imminent for many countries, and protecting Connectwise Automate from such attacks is on the mind of many MSPs. Below we discuss some background on the threat, and what MSPs can do to defend ConnectWise Automate in a cyberwar. Cyberwar: Are MSPs a target? As […]
How to pwn an Automate server: Connectwise Automate LAN Security

ConnectWise Automate security is something at the forefront of discussion for every MSP. Previously we’ve discussed security from the WAN angle, and how reverse proxy technology can be implemented to reduce the attack surface. However, internal LAN communications can also be an attack vector, and here at Automation Theory, we wanted to give proper attention […]
MySQL for Automate 101: Facilitating Custom Integrations

Leveraging the database of Automate can be intimidating, especially for partners who don’t have previous database experience. With the release of our new plugin Database Commander, we wanted to create an introductory guide to using MySQL in Automate, and simultaneously demonstrate the features of the plugin. Please note that you can use any MySQL query […]